Norway Database Breach: 1.3M Records Allegedly Exposed

➤Summary
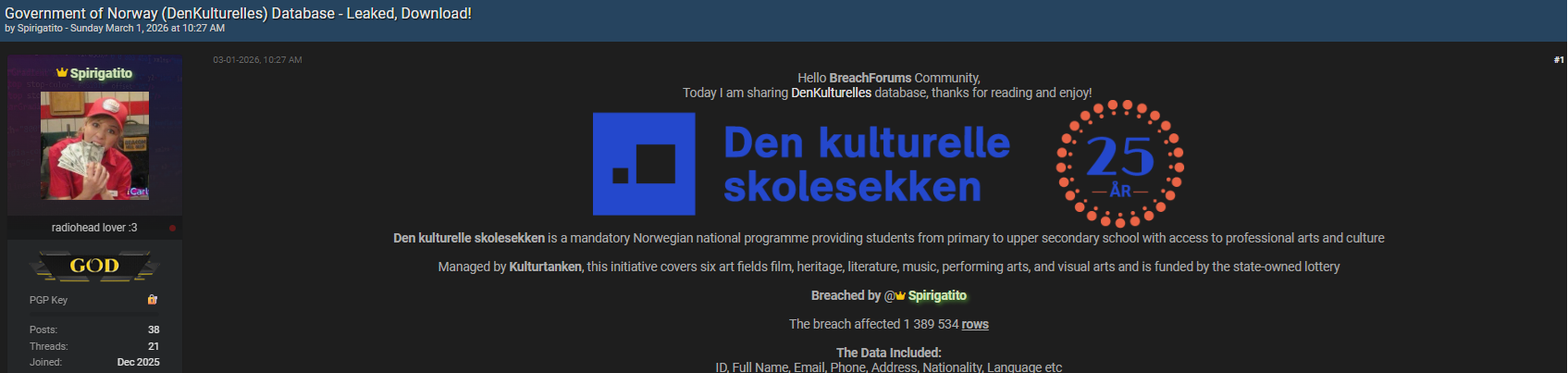
The Norway database breach allegedly involving the Government of Norway’s cultural platform DenKulturelles has sparked major cybersecurity concerns after a threat actor claimed to leak sensitive citizen information online. Posted on BreachForums.as by a user known as Spirigatito on March 1, 2026, the dataset reportedly contains over 1.3 million records including personally identifiable information (PII). If verified, this incident represents a significant exposure affecting individuals connected to cultural programs and public databases.
Data leaks of this scale highlight the growing risks associated with public-sector digital infrastructure and the increasing role of underground forums in distributing stolen information. Understanding the scope, risks, and defensive measures surrounding this alleged incident is critical for organizations and individuals alike. 🚨
Overview of the Alleged Data Leak
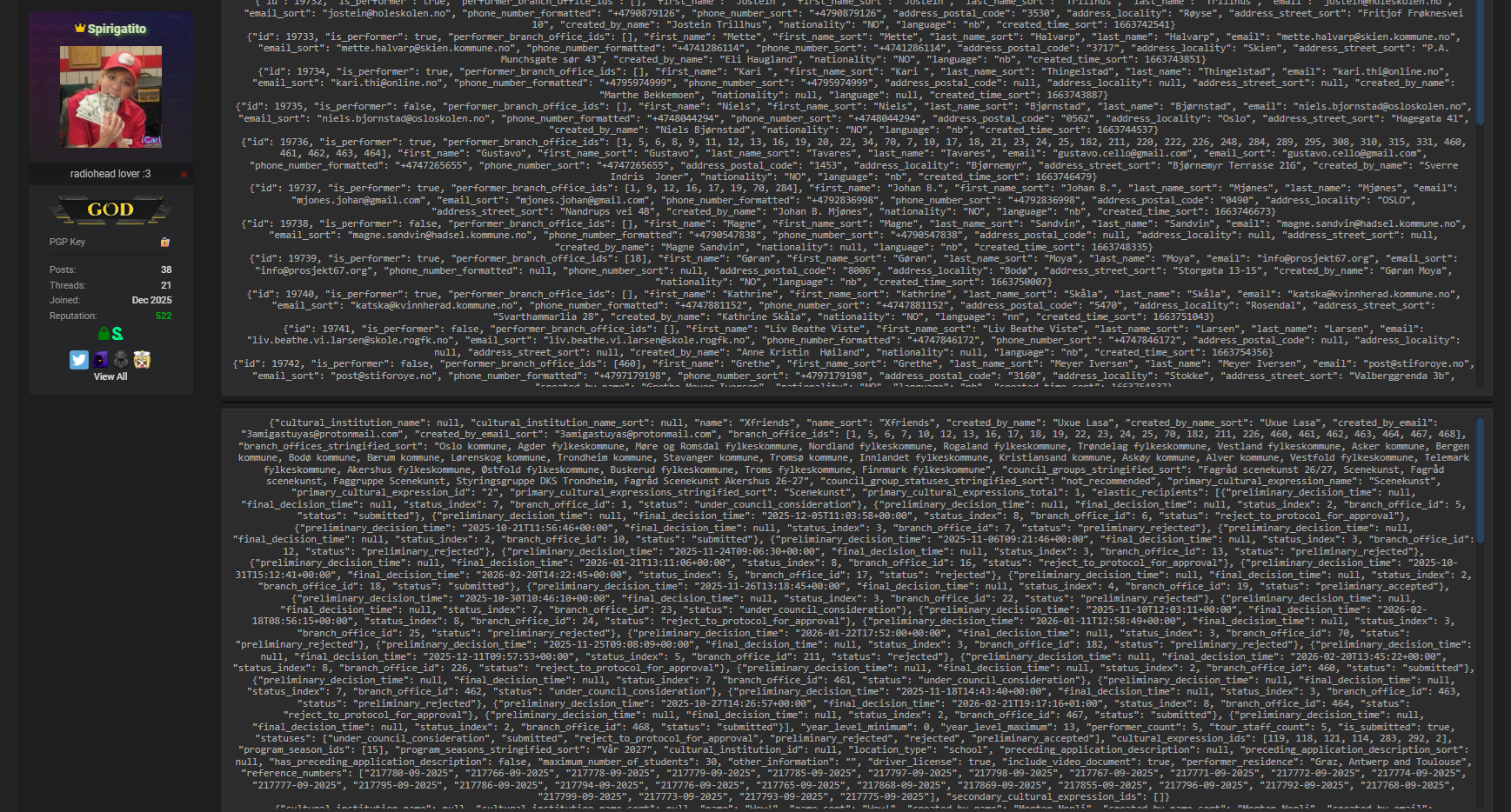
According to the forum publication, the Norway database breach involves an alleged compromise of DenKulturelles, a cultural initiative linked to government services. The threat actor claimed access to a database containing 1,389,534 rows of structured records.
Reported compromised data fields include:
- ID numbers
- Full names
- Email addresses
- Phone numbers
- Residential addresses
- Nationality information
- Language preferences
Such datasets are particularly valuable to cybercriminals because they enable identity profiling and targeted fraud campaigns. The leak was advertised on BreachForums.as, a well-known cybercrime marketplace used for distributing stolen databases and breach announcements.
Cybersecurity observers note that forum posts alone do not confirm authenticity, but they often signal early indicators of real incidents requiring investigation. 🔎
Timeline of Events
Below is a simplified timeline summarizing available information:
| Event | Details |
| Forum | BreachForums.as |
| Author | Spirigatito |
| Publication Date | March 1, 2026 |
| Alleged Victim | DenKulturelles (Government of Norway) |
| Records Claimed | 1,389,534 rows |
| Data Type | Personal identifiable information |
| Threat intelligence teams typically monitor underground forums continuously to detect early breach disclosures before public confirmation. | |
| Organizations often rely on intelligence platforms explained here: https://darknetsearch.com/dark-web-monitoring/. |
Why Government Databases Are High-Value Targets
Public-sector databases are increasingly targeted because they contain verified citizen information. Unlike random datasets, government records carry high credibility, making them extremely useful for identity theft and fraud.
Common attacker motivations include:
- Financial fraud and impersonation
- Social engineering campaigns
- Credential stuffing attacks
- Political or ideological objectives
In some cases, attackers linked to nation-state threats may exploit data exposures for intelligence gathering rather than immediate profit.
The alleged Norway database breach illustrates how cultural or educational platforms can become unexpected entry points into broader government ecosystems. 🧠
Potential Risks for Affected Individuals
If the claims prove accurate, exposed individuals may face several risks.
Primary threats:
- Phishing emails using real personal data
- SIM-swap attempts via exposed phone numbers
- Identity fraud applications
- Targeted scams using nationality or language details
Because attackers possess contextual information, messages appear highly convincing.
Practical tip ✅: Anyone potentially affected should enable account alerts and verify communications directly through official government channels rather than responding to unsolicited emails.
How Breach Forums Amplify Cybercrime
Underground forums like BreachForums function as distribution hubs for leaked data. Threat actors post samples to build credibility before selling or releasing full datasets.
Typical workflow:
- Data obtained via intrusion or misconfiguration.
- Sample uploaded to forum thread.
- Buyers validate authenticity.
- Dataset monetized or publicly released.
The alleged leak demonstrates how quickly sensitive information can spread globally once posted online.
Security analysts emphasize the importance of proactive monitoring and early detection using specialized threat intelligence services and automated alerts. 🛡️
Question: Does a Forum Post Mean the Breach Is Confirmed?
No. A forum claim does not automatically confirm a breach.
However, it serves as an early warning signal. Security teams treat such posts as indicators requiring validation through forensic analysis, official statements, or independent verification.
This is why monitoring underground activity has become essential to modern cybersecurity operations.
The Role of Dark Web Intelligence in Early Detection
Organizations increasingly depend on monitoring technologies to detect exposures before widespread exploitation occurs.
Key capabilities include:
- Tracking leaked databases
- Monitoring hacker discussions
- Detecting credential sales
- Generating actionable alerts
Many enterprises deploy a dark web monitoring solution to identify compromised data tied to employees or customers shortly after publication.
Security providers also produce dark web monitoring reports that help organizations understand exposure scope and prioritize incident response.
Managed security providers increasingly implement Dark Web Monitoring for MSSP environments to protect multiple clients simultaneously.
You can explore proactive threat detection strategies at Darknetsearch.com.
Although the exact method remains unconfirmed, similar incidents often result from:
- Misconfigured cloud databases
- Weak authentication controls
- API exposure vulnerabilities
- Credential reuse attacks
- Unpatched software systems
These weaknesses allow attackers to extract structured datasets without triggering alarms.
According to cybersecurity guidance published by the National Institute of Standards and Technology (NIST), strong access control and continuous monitoring significantly reduce breach probability.
The Norway database breach highlights how even non-critical platforms can expose large amounts of sensitive data when security hygiene fails. ⚠️
Checklist: How Organizations Can Reduce Exposure Risk
Use this security checklist to minimize breach impact:
✔ Implement least-privilege access controls
✔ Monitor database access logs continuously
✔ Encrypt stored personal information
✔ Deploy anomaly detection systems
✔ Conduct regular penetration testing
✔ Monitor underground forums for leaked data
Following these practices helps organizations detect compromises faster and limit data exfiltration.
Impact on Privacy and Public Trust
Government-related data incidents often carry broader societal consequences. Citizens expect public institutions to safeguard personal information responsibly.
When large datasets appear online, trust erosion occurs even before confirmation.
Possible long-term effects include:
- Reduced participation in digital public services
- Increased regulatory scrutiny
- Legal investigations
- Mandatory transparency reporting
Cybersecurity experts stress that rapid communication and transparent investigation are essential to restoring confidence after alleged breaches. 📊
Emerging Trends in Public Sector Cybersecurity
The incident reflects several growing cybersecurity trends:
- Increased targeting of public databases
- Data leaks announced first on underground forums
- Monetization of personal datasets
- Hybrid financially motivated and geopolitical attacks
Security analysts warn that attackers are shifting from random targets to structured national datasets due to their long-term value.
As digital transformation expands, public institutions must balance accessibility with stronger security controls. 🔐
Expert Insight
One threat intelligence analyst summarized the evolving landscape:
“Modern breaches are discovered on criminal forums before official disclosures. Monitoring these environments is now a core defensive requirement.”
This perspective reinforces the importance of proactive intelligence rather than reactive response strategies.
How Individuals Can Protect Themselves After a Data Leak
If you suspect exposure:
- Change passwords immediately
- Enable multi-factor authentication
- Monitor financial statements
- Watch for targeted phishing messages
- Use identity monitoring services
Even without confirmation, preventive action significantly reduces risk exposure.
Conclusion: Why Early Awareness Matters
The alleged Norway database breach involving DenKulturelles demonstrates how quickly sensitive information can surface within cybercriminal ecosystems. Whether fully verified or still under investigation, the exposure claim underscores a critical reality: data leaks increasingly emerge first on underground forums, giving attackers a time advantage over defenders. Organizations must adopt continuous monitoring, intelligence-driven defenses, and proactive response strategies to stay ahead of evolving threats. Individuals, meanwhile, should remain vigilant against phishing and identity fraud attempts following large-scale breach claims. Awareness, monitoring, and rapid action remain the strongest defenses in today’s threat landscape. 🚨
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →

