DIAN Data Leak Revealed: 7 Key Facts You Must Know

➤Summary
The DIAN data leak allegedly published on an underground cybercrime forum has raised serious cybersecurity concerns across Latin America. According to a post shared on Breachforums.as by user ArcRaidersPlayer on March 2, 2026, sensitive records tied to the Colombian government appointment platform AGENDAMIENTO.DIAN.GOV.CO may have been exposed and offered for sale. The incident highlights growing risks affecting public-sector digital services and demonstrates how government portals remain attractive targets for threat actors. Dark web reports claim the database includes identity validation information, personal details, emails, and phone numbers — data categories frequently leveraged in fraud and identity theft campaigns. While official confirmation remains pending, the alleged exposure illustrates why proactive data breach detection strategies are essential for modern institutions. ⚠️
What Is the Alleged DIAN Platform Incident?
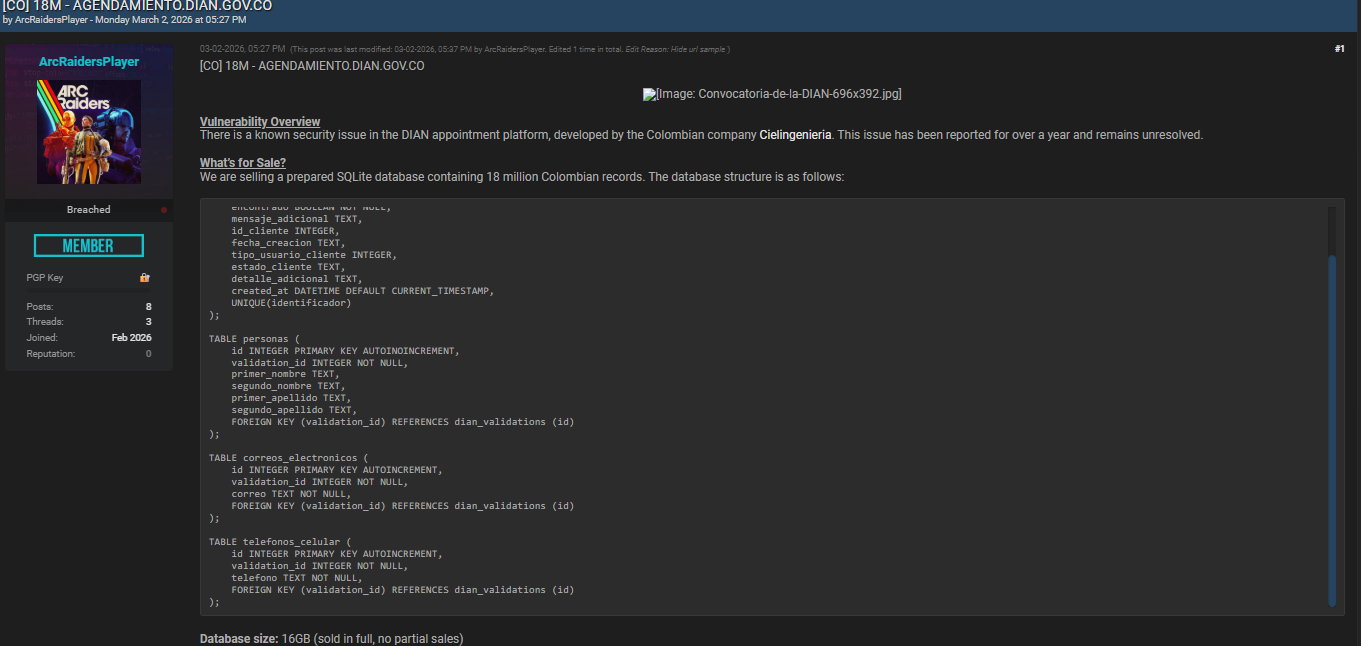
The reported DIAN data leak centers on AGENDAMIENTO.DIAN.GOV.CO, an appointment scheduling platform used by Colombia’s tax authority (DIAN). The forum listing claims attackers exploited a vulnerability reportedly known for more than a year within software developed by Colombian company Cielingenieria.
According to the seller, the dataset is priced at $2,000 USD (negotiable) and allegedly contains structured database tables extracted from the system backend. Such listings are common indicators identified through dark web intelligence operations, where stolen databases are monetized shortly after exfiltration. 💻
Cybercriminal marketplaces often serve as early warning signals for organizations before incidents become public. Platforms like DarknetSearch monitoring solutions specialize in identifying compromised assets circulating in underground communities, helping companies react faster.
Translated Database Structure (English Version)
Below is the translated version of the allegedly compromised database schema shared in the forum post.
Table: dian_validations
| Field | Meaning |
| id | Unique record identifier |
| identificador | Identification number |
| tipo_identificacion | Identification type |
| encontrado | Whether the person was found/validated |
| mensaje_adicional | Additional message |
| id_cliente | Client ID |
| fecha_creacion | Creation date |
| tipo_usuario_cliente | Client user type |
| estado_cliente | Client status |
| detalle_adicional | Additional details |
| created_at | Timestamp automatically generated |
| UNIQUE(identificador) | Prevents duplicate IDs |
Table: personas
| Field | Meaning |
| id | Unique record identifier |
| validation_id | Linked validation record |
| primer_nombre | First name |
| segundo_nombre | Middle name |
| primer_apellido | Last name |
| segundo_apellido | Second last name |
Table: correos_electronicos
| Field | Meaning |
| id | Unique record identifier |
| validation_id | Linked validation |
| correo | Email address |
Table: telefonos_celular
| Field | Meaning |
| id | Unique record identifier |
| validation_id | Linked validation |
| telefono | Mobile phone number |
| If authentic, this structure suggests exposure of personally identifiable information (PII), a category frequently abused for phishing, SIM swapping, and tax fraud schemes. |
Why Government Platforms Are Increasingly Targeted
Government digital portals store large volumes of verified citizen data, making them high-value targets. Attackers focus on systems where identity validation occurs because the data is already authenticated and highly reliable.
Security experts consistently warn that unresolved vulnerabilities dramatically increase breach risk. According to guidance published by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), organizations must isolate affected systems and initiate coordinated response procedures immediately after suspected compromise.
The alleged DIAN data leak demonstrates three recurring attack patterns:
- Long-standing vulnerabilities left unpatched
- Third-party development risks
- Insufficient Government Domain Monitoring practices
When public-sector infrastructure lags behind threat evolution, attackers exploit the gap quickly. 🌐
How Threat Actors Monetize Stolen Databases
Cybercriminals rarely leak data immediately. Instead, they:
- Extract databases silently.
- Verify records for resale value.
- Offer access privately before public exposure.
- Bundle datasets with other breaches.
This commercialization model explains why early discovery through a darkweb monitoring platform can drastically reduce downstream damage.
Organizations leveraging proactive monitoring — such as insights available through Darknet exposure analysis tools — can identify compromised assets even before widespread media coverage.
Real Risks for Citizens and Institutions
If confirmed, the DIAN data leak could enable:
- Identity impersonation
- Targeted phishing campaigns
- Tax refund fraud
- Credential stuffing attacks
- Social engineering operations
One cybersecurity analyst summarized the risk clearly:
“Validated identity datasets are significantly more dangerous than random leaks because attackers trust the accuracy.”
Government records hold long-term value, meaning exposed data may circulate for years. 🔐
Question: Does a Forum Listing Always Mean a Real Breach?
Short answer: No — but it must always be investigated.
Some listings exaggerate claims, yet many major incidents first appeared on underground forums before confirmation. Analysts therefore treat every credible listing as a potential incident requiring verification.
Practical Checklist: How Organizations Should Respond
Here’s a quick response framework aligned with global cybersecurity guidance:
✅ Investigate exposed domains immediately
✅ Verify database access logs
✅ Patch known vulnerabilities
✅ Reset authentication tokens
✅ Notify affected stakeholders
✅ Monitor underground marketplaces continuously
CISA recommends preserving forensic evidence and isolating impacted systems to prevent further compromise. (CISA)
This approach strengthens both incident containment and regulatory compliance.
The Role of Continuous Monitoring in Preventing Future Incidents
Modern cybersecurity increasingly depends on early warning intelligence rather than reactive defense. Continuous scanning across hidden networks enables organizations to detect references to internal assets before attackers escalate exploitation.
Solutions combining automated alerts, analyst verification, and external threat visibility — like those discussed in dark web monitoring resources — help security teams track emerging risks proactively.
The inclusion of identity records in the alleged DIAN data leak reinforces the importance of integrated monitoring strategies that combine vulnerability management, intelligence gathering, and incident readiness. 🧠
Broader Cybersecurity Lessons From the Incident
Even without official confirmation, the situation highlights critical lessons:
- Known vulnerabilities must never remain unresolved.
- Public digital services require constant auditing.
- Third-party vendors introduce shared risk.
- Threat intelligence must extend beyond internal networks.
Government agencies worldwide increasingly invest in advanced monitoring because cybercriminal ecosystems evolve faster than traditional defenses.
Organizations adopting layered visibility — including network telemetry, intelligence feeds, and breach surveillance — significantly reduce response time.
Conclusion: Why the Alleged DIAN Data Leak Matters
The alleged DIAN data leak serves as a reminder that government platforms are not immune to cyber threats. Whether ultimately verified or disproven, the listing demonstrates how quickly sensitive information can appear in underground markets and how damaging delayed remediation can become.
Cybersecurity today depends on anticipation rather than reaction. Monitoring external threat environments, validating vulnerabilities quickly, and strengthening incident readiness are no longer optional — they are operational necessities. 🚨
Businesses and institutions that invest in proactive monitoring gain visibility where attackers operate first, dramatically improving resilience against emerging threats.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →

