Team4Security Data Breach: 7 Urgent Facts Revealed

➤Summary
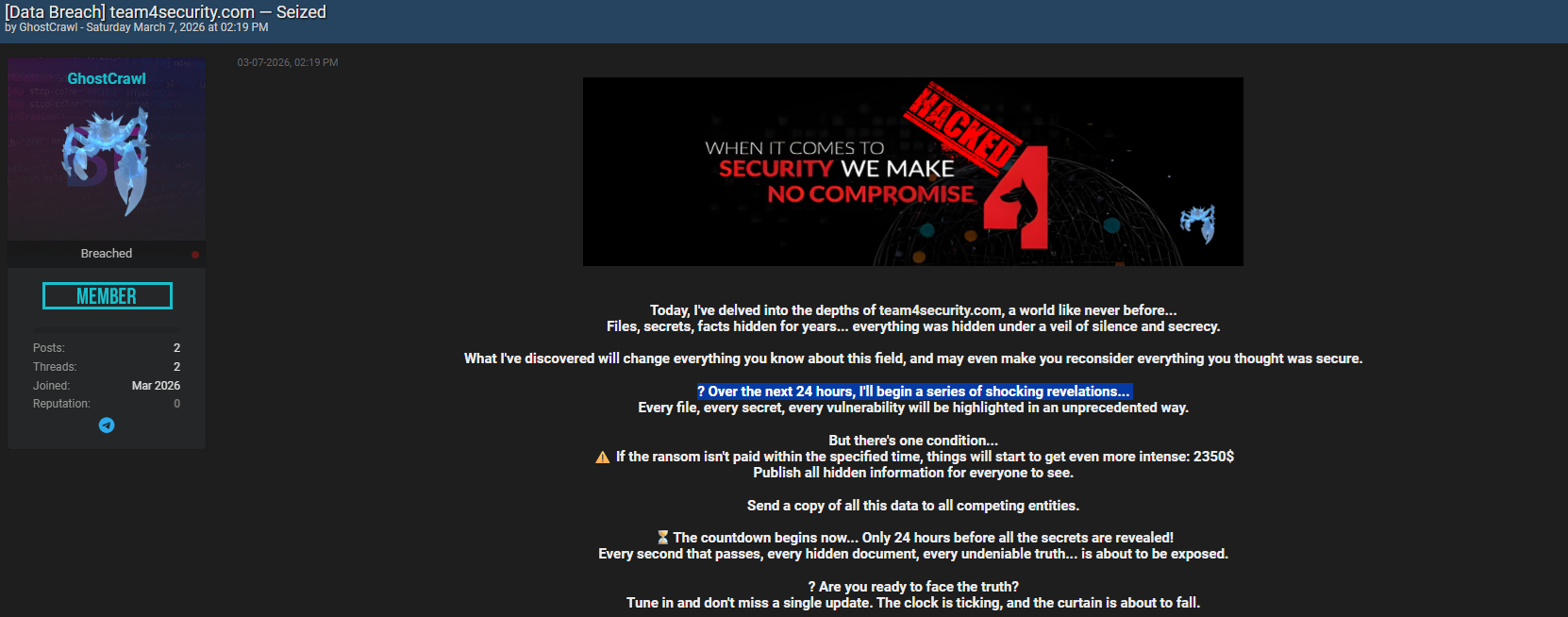
Team4Security data breach allegations surfaced online after a controversial post appeared on Breachforums.as on March 7, 2026, authored by a user known as “GhostCrawl.” The message claimed access to confidential files, hidden vulnerabilities, and sensitive information allegedly extracted from team4security.com. The announcement quickly gained traction among cybersecurity researchers, threat analysts, and organizations monitoring hacker forums. While the claims remain unverified, the post introduced a ransom demand and a countdown threatening full disclosure within 24 hours, sparking widespread concern across the cybersecurity community. 🚨
This darknetsearch.com article examines what is currently known, analyzes the credibility of the claims, explains the potential impact, and outlines how businesses should respond when facing similar incidents. As online threats evolve, understanding how alleged breaches unfold is critical for risk awareness and proactive defense.
What Happened: Overview of the Alleged Incident
On March 7, 2026, a forum thread appeared on Breachforums.as authored by GhostCrawl, describing a supposed infiltration into team4security.com systems. The post included dramatic language suggesting the discovery of “files, secrets, facts hidden for years,” along with a ransom demand of $2,350.
According to the author, failure to pay would result in:
- Public release of all obtained information
- Distribution of data to competing entities
Progressive exposure of vulnerabilities
The message framed the event as a staged revelation campaign rather than a single leak, which is a tactic sometimes used in ransomware-style extortion cases. Analysts classify such announcements as early-warning signals of a potential cybersecurity breach, though verification requires independent confirmation.
The tone and structure resemble previous cyberattack announcements seen across underground forums, where threat actors attempt to build pressure through psychological tactics and public visibility.
Timeline of Events
Below is a simplified breakdown useful for quick understanding:
| Date | Event |
| March 7, 2026 | Forum post published by GhostCrawl |
| Same day | Ransom demand issued |
| +24 hours | Threatened disclosure deadline |
| Ongoing | Community monitoring and investigation |
| This format mirrors many modern ransomware disclosures, where attackers leverage urgency to force negotiation decisions. ⏳ |
The Ransom Message Explained
The author’s statement emphasized secrecy, hidden truths, and imminent exposure. While sensational wording is common in hacker forums, it serves strategic purposes:
- Creating media attention
- Increasing perceived credibility
- Pressuring organizations publicly
- Attracting buyers for leaked data
One key question arises: Does a public ransom post confirm a real breach?
Answer: No. Public claims alone do not confirm a compromise; technical validation, forensic evidence, or official acknowledgment are required.
Security researchers often treat such posts as intelligence leads rather than proof.
Why Hacker Forums Play a Central Role
Underground communities act as marketplaces and communication hubs for threat actors. Breachforums, historically associated with leaked databases and vulnerability disclosures, has become a monitoring priority for investigators.
Organizations increasingly rely on Dark web monitoring platforms to identify early signs of compromise before data becomes widely distributed. These platforms scan forums, marketplaces, and encrypted channels for mentions of corporate assets or stolen credentials. 🔎
The growing visibility of these forums means alleged incidents like this can spread globally within hours, amplifying reputational risk even before confirmation.
Potential Risks if the Claims Are True
If the Team4Security data breach allegations were verified, several impacts could follow:
- Exposure of internal documents
- Credential leaks affecting clients
- Competitive intelligence loss
- Regulatory consequences
- Operational disruption
These outcomes align with patterns seen in modern cybersecurity breach scenarios worldwide. Even small ransom amounts can mask larger strategic motives, such as reputation damage or vulnerability exposure.
According to guidance from the Cybersecurity and Infrastructure Security Agency (CISA), organizations should treat extortion threats as active incidents requiring investigation and containment measures (https://www.cisa.gov).
The possibility of leaked data being shared with competitors adds an unusual dimension, suggesting economic pressure rather than purely financial motivation.
How Experts Evaluate Alleged Breaches
Cybersecurity professionals typically assess credibility using several indicators:
- Proof-of-data samples
- Screenshots or hashes
- Known vulnerability references
- Independent confirmations
- Communication consistency
An anonymous threat intelligence analyst noted:
“Public claims are often exaggerated, but ignoring them entirely can delay incident response.”
This balanced approach prevents both panic and complacency. 🛡️
Modern data breach detection processes involve automated log analysis, anomaly monitoring, and threat intelligence correlation to validate whether intrusion activity occurred.
Practical Checklist: What Organizations Should Do
When a similar claim appears online, organizations should immediately follow a structured response:
✅ Verify whether systems show unusual access patterns
✅ Conduct internal log reviews
✅ Reset privileged credentials
✅ Activate incident response teams
✅ Monitor underground forums for updates
✅ Communicate transparently with stakeholders
Early action can dramatically reduce long-term consequences and support stronger data protection practices across infrastructure.
The Psychology Behind Countdown Threats
Countdown timers are a psychological strategy frequently used in ransomware communications. They:
- Increase urgency
- Limit decision-making time
- Encourage rapid payment
- Amplify media attention
This technique often leads to emotional responses rather than strategic evaluation. Organizations are advised to rely on incident response frameworks rather than reacting solely to attacker deadlines. ⚠️
In many historical cyberattack cases, countdown threats were extended repeatedly, indicating negotiation leverage rather than fixed timelines.
Industry Trends: Why Alleged Breaches Are Increasing
Several factors explain the rise in publicly announced incidents:
- Growth of ransomware-as-a-service ecosystems
- Monetization of stolen information
- Increased corporate digital exposure
- Competitive intelligence targeting
- Publicity-driven hacker reputations
The alleged Team4Security data breach reflects broader industry trends where attackers seek visibility as much as financial gain.
Could This Be a Hoax?
Yes, and it happens frequently. Some forum posts are designed to:
- Gain notoriety
- Manipulate markets
- Scam buyers
- Test organizational responses
Without leaked samples or technical validation, analysts classify such events as unconfirmed threat claims.
However, ignoring them entirely may expose organizations to delayed mitigation if the threat proves real. Balanced vigilance remains essential. 🤔
Long-Term Implications for Cybersecurity
Whether verified or not, the alleged Team4Security ransomware incident highlights how reputational risk now spreads faster than technical confirmation. Public perception can shift instantly once a breach narrative appears online.
Companies must prepare not only for intrusions but also for information warfare, where claims alone influence trust and credibility.
Modern strategies combine:
- Threat intelligence monitoring
- Incident readiness planning
- Employee awareness training
- Continuous vulnerability assessments
These measures help organizations respond confidently even amid uncertainty.
Key Takeaways (Featured Snippet Summary)
Main facts about the incident:
- Allegation posted March 7, 2026
- Author: GhostCrawl
- Platform: Breachforums.as
- Ransom demand: $2,350
- 24-hour disclosure threat
- No official confirmation yet
This concise overview helps readers quickly understand the situation while deeper investigations continue.
Conclusion: Staying Ahead of Emerging Threats
The Team4Security data breach allegations demonstrate how rapidly cyber threats evolve and how public claims alone can trigger widespread concern. Whether the incident proves legitimate or not, it reinforces an important lesson: organizations must assume visibility in underground communities and prepare proactive defenses. 🔐
Monitoring early warning signals, verifying claims carefully, and maintaining strong response frameworks are now essential components of modern cybersecurity resilience. As threat actors increasingly weaponize publicity and pressure tactics, awareness becomes just as critical as technology.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.


