Starbucks Data Breach Allegation: Key Risks Revealed

➤Summary
The alleged Starbucks data breach posted on a cybercrime forum has raised serious concerns across cybersecurity communities and enterprise risk teams. On April 1, 2026, a threat actor known as BlackVortex1 published claims on darkforums.su stating that proprietary operational technology, internal software systems, and development assets belonging to Starbucks had been compromised. While the breach remains unverified, the detailed description of files suggests potential exposure of sensitive infrastructure components rather than customer payment data. Security analysts warn that incidents like this demonstrate how attackers increasingly target corporate technology ecosystems instead of traditional databases. The case also highlights why organizations must adopt dark web surveillance and proactive intelligence strategies to identify threats before leaks occur. If confirmed, this event could represent a significant operational security risk rather than a conventional consumer data breach. 🚨
What Was Allegedly Posted on DarkForums.su
According to the forum post, the attacker claims access to multiple internal environments tied to Starbucks’ global store operations. The listing categorized the data into several technical areas, suggesting a structured exfiltration rather than random leakage.
The post included a ransom-style warning: Starbucks allegedly had until April 5, 2026 at 5:00 PM before full data release.
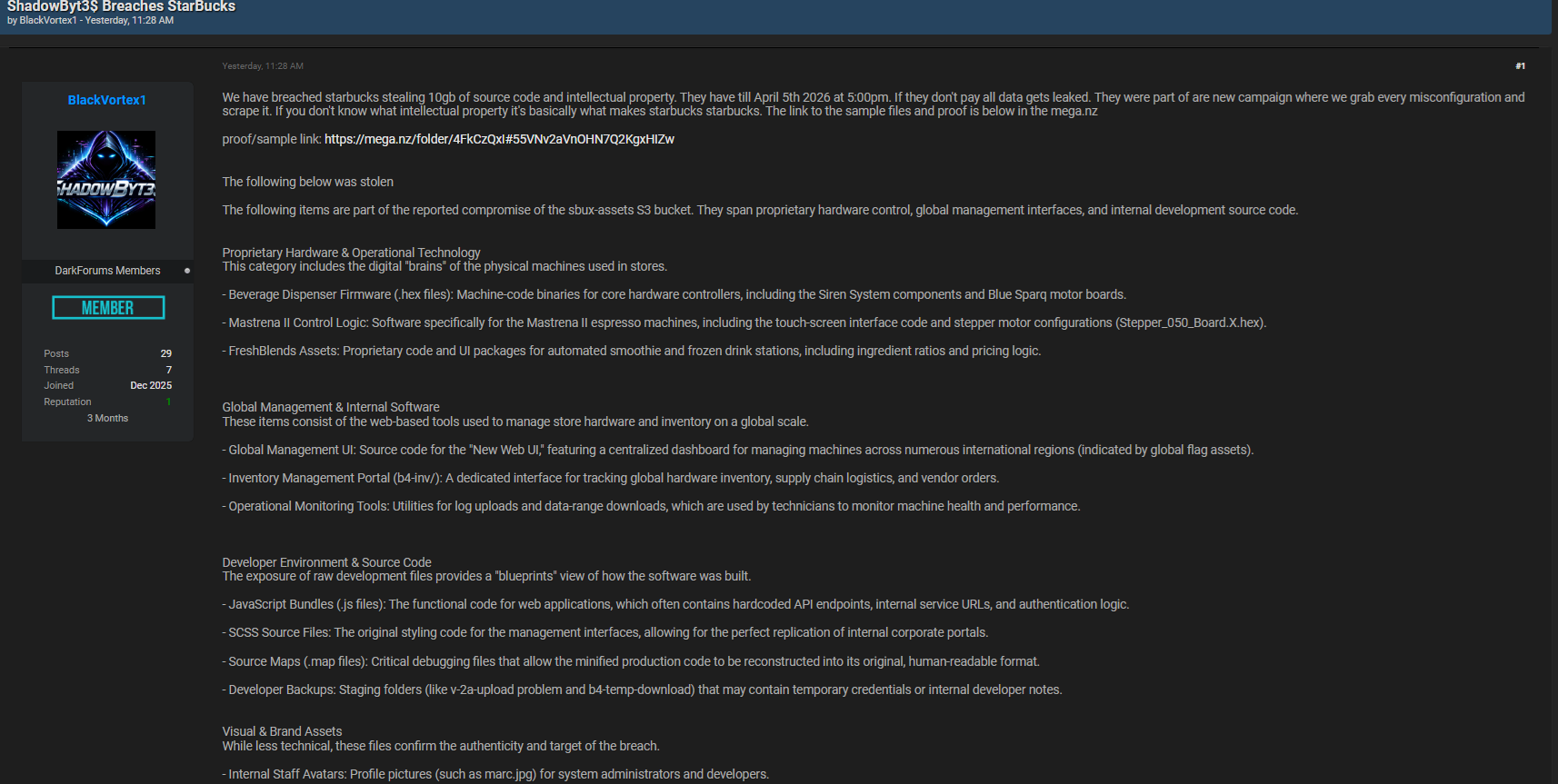
The claimed assets include operational firmware, internal dashboards, development files, and branding resources—indicating potential exposure of internal infrastructure rather than customer records.
Cybercriminal forums frequently host exaggerated claims, but the level of technical specificity makes this allegation notable. Analysts emphasize that monitoring underground discussions through dark web surveillance is often the first indicator of emerging corporate threats. 🔍
Proprietary Hardware and Operational Technology Exposure
One of the most concerning aspects involves operational technology (OT) tied directly to in-store machines.
The actor claims possession of:
• Beverage dispenser firmware (.hex binaries)
• Siren System components and Blue Sparq motor boards
• Mastrena II espresso machine control logic
• Stepper motor configurations and touchscreen interfaces
• FreshBlends automation software with ingredient ratios and pricing logic
If authentic, these assets could expose how physical machines operate globally. Attackers could potentially analyze firmware to discover vulnerabilities or replicate proprietary systems.
Operational technology attacks are increasingly common because they impact real-world infrastructure—not just digital assets. ⚙️
Internal Management Platforms and Global Software Tools
The alleged leak also references centralized management systems used to operate Starbucks locations worldwide.
Claimed materials include:
• Global Management UI source code
• International machine monitoring dashboards
• Inventory Management Portal (b4-inv/)
• Supply chain and vendor order interfaces
• Operational monitoring utilities for technician diagnostics
Such platforms typically control device updates, inventory tracking, and performance analytics across regions.
Exposure of these systems could allow attackers to map internal architecture or identify privileged access points.
This type of risk underscores why enterprises deploy real-time dark web monitoring solution platforms to detect early warning signs before threat actors escalate demands.
Developer Environment Files: Why Source Code Exposure Matters
Perhaps the most sensitive category involves developer resources described as “blueprints” of internal systems.
The forum post lists:
• JavaScript application bundles containing API endpoints
• SCSS styling source files enabling portal replication
• Source maps capable of reconstructing readable code
• Developer backup folders with possible credentials
Source maps are particularly dangerous because they allow attackers to reverse-engineer applications easily.
Security experts often warn that exposed development artifacts can accelerate exploitation timelines dramatically.
A cybersecurity analyst once noted: “Source code exposure shortens attacker research from months to hours.” 💻
Visual and Brand Assets Confirm Target Authenticity
While less technical, branding materials strengthen the credibility of the claim.
The post allegedly includes:
• Internal staff avatars
• Administrator profile images
• High-resolution Starbucks corporate logos
• Vendor branding assets used internally
These files do not create direct system risk but help attackers build convincing phishing campaigns or impersonation portals.
Brand-based attacks frequently follow dark web leaks, making early detection essential for organizations seeking to protect business from dark web threats.
Why Cybercriminals Use Dark Web Forums for Extortion
Dark web forums serve as negotiation and publicity platforms for attackers.
Common objectives include:
- Pressuring victims into ransom payments
- Proving breach legitimacy to buyers
- Attracting collaborators or brokers
- Increasing media attention
The alleged Starbucks data breach follows a pattern seen in modern cyber extortion campaigns where threat actors announce leaks before releasing data.
Monitoring these environments through platforms like dark web monitoring platforms allows organizations to identify threats during early exposure stages. 🕵️
Key Risks Businesses Should Understand
Even without confirmed customer data exposure, operational leaks create serious risks.
| Risk Type | Potential Impact |
| Operational disruption | Machine malfunction analysis |
| Intellectual property theft | Competitor replication |
| Supply chain exposure | Vendor targeting |
| Phishing expansion | Brand impersonation |
| Infrastructure mapping | Future cyberattacks |
| This demonstrates why dark web intelligence has become a critical component of modern cybersecurity strategy. |
Practical Checklist: How to Respond to Alleged Dark Web Breaches
Organizations should follow this response checklist:
✅ Validate claims through threat intelligence teams
✅ Monitor underground forums continuously
✅ Rotate credentials linked to development environments
✅ Audit exposed APIs and endpoints
✅ Prepare incident communication plans
✅ Deploy dark web surveillance tools immediately
A proactive response can reduce damage even before confirmation occurs. 📊
The Role of Real-Time Dark Web Monitoring
A real-time dark web monitoring solution enables organizations to detect mentions of their brand, infrastructure, or stolen assets across underground communities automatically.
Core benefits include:
• Early breach detection
• Threat actor tracking
• Leak verification support
• Credential exposure alerts
• Brand abuse prevention
Learn more about monitoring strategies at Darknetsearch.com
According to cybersecurity guidance published by the Cybersecurity & Infrastructure Security Agency (CISA), organizations should actively monitor threat intelligence sources to detect emerging risks early. 🛡️
Question Many Organizations Ask
Does a dark web post automatically mean a breach is real?
No. Many claims are exaggerated or fabricated. However, credible technical details significantly increase the likelihood that at least partial data exposure occurred, which is why investigation and monitoring must begin immediately.
Emerging Trend: Operational Technology as a Target
The alleged Starbucks data breach reflects a broader shift toward targeting operational technology ecosystems.
Attackers increasingly focus on:
• Smart retail devices
• IoT-enabled equipment
• Global management dashboards
• Remote maintenance tools
These environments often receive less security attention than financial databases, making them attractive targets.
Organizations must combine endpoint security, brand monitoring, and dark web surveillance to maintain visibility across both digital and physical attack surfaces. ⚠️
How DarknetSearch Helps Protect Businesses
DarknetSearch provides intelligence tools designed to protect business from dark web threats by identifying risks before they escalate.
Capabilities include:
• Continuous dark web surveillance
• Automated leak detection
• Threat actor tracking
• Credential exposure alerts
• Enterprise investigation workflows
Early intelligence enables security teams to respond before public disclosure or operational disruption occurs. 🚀
Conclusion: Allegations Highlight the Need for Proactive Intelligence
Whether confirmed or not, the alleged Starbucks data breach demonstrates how cybercriminal activity increasingly unfolds publicly on underground forums before organizations even detect incidents internally. Operational technology exposure, developer files, and internal dashboards represent high-value targets capable of enabling future attacks.
Businesses can no longer rely solely on perimeter defenses. Continuous dark web surveillance, proactive intelligence gathering, and deployment of a real-time dark web monitoring solution are essential to modern cyber resilience.
Organizations that actively monitor underground ecosystems are far better positioned to prevent escalation, protect intellectual property, and respond quickly to emerging threats. 🔐
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

