EquityBrix Data Leak: 152M Records Exposure Revealed

➤Summary
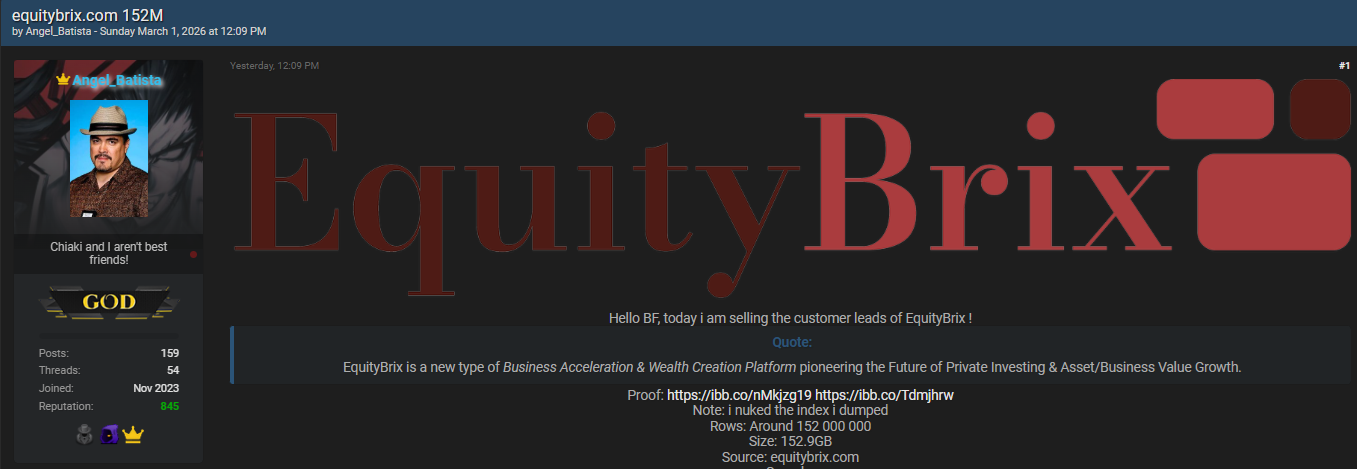
The EquityBrix data leak has surfaced as one of the most significant alleged cybersecurity incidents reported in early 2026, raising concerns across the threat-intelligence community. According to monitoring conducted by the Kaduu team, a massive database allegedly linked to equitybrix.com appeared on the underground forum Breachforums.as on 01 March 2026, posted by threat actor Angel_Batista. The dataset reportedly contains around 152 million rows and weighs approximately 152.9GB, suggesting a large-scale exposure of consumer prospect data.
This discovery highlights how modern cybercrime ecosystems operate and why continuous dark web monitoring has become essential for organizations worldwide. While verification processes are still ongoing, early analysis indicates structured personal and demographic records that could pose privacy, fraud, and reputational risks if validated. 🚨
Below is a detailed breakdown of what is currently known, the potential impact, and how companies can respond proactively.
What We Know About the Alleged EquityBrix Incident
According to intelligence gathered during routine surveillance, the database listing appeared publicly within Breachforums.as — a forum historically associated with leaked datasets and cybercriminal trading activity. The post allegedly claimed the source as equitybrix.com, presenting structured JSON records indicative of marketing or prospect enrichment datasets.
Key reported details:
- Forum: Breachforums.as
- Actor: Angel_Batista
- Publication date: 01 March 2026
- Estimated rows: ~152,000,000
- Dataset size: 152.9GB
- Source claimed: equitybrix.com
The Kaduu team identified the listing during automated monitoring operations designed to detect emerging exposures across underground communities.
Such discoveries often represent early warning signals before wider exploitation begins. 🔎
The structure of the dataset suggests indexing consistent with large analytics or consumer intelligence platforms.
Example of the Compromised Records
Samples shared alongside the listing demonstrate structured consumer entries containing identity, location, demographic, and financial indicators.
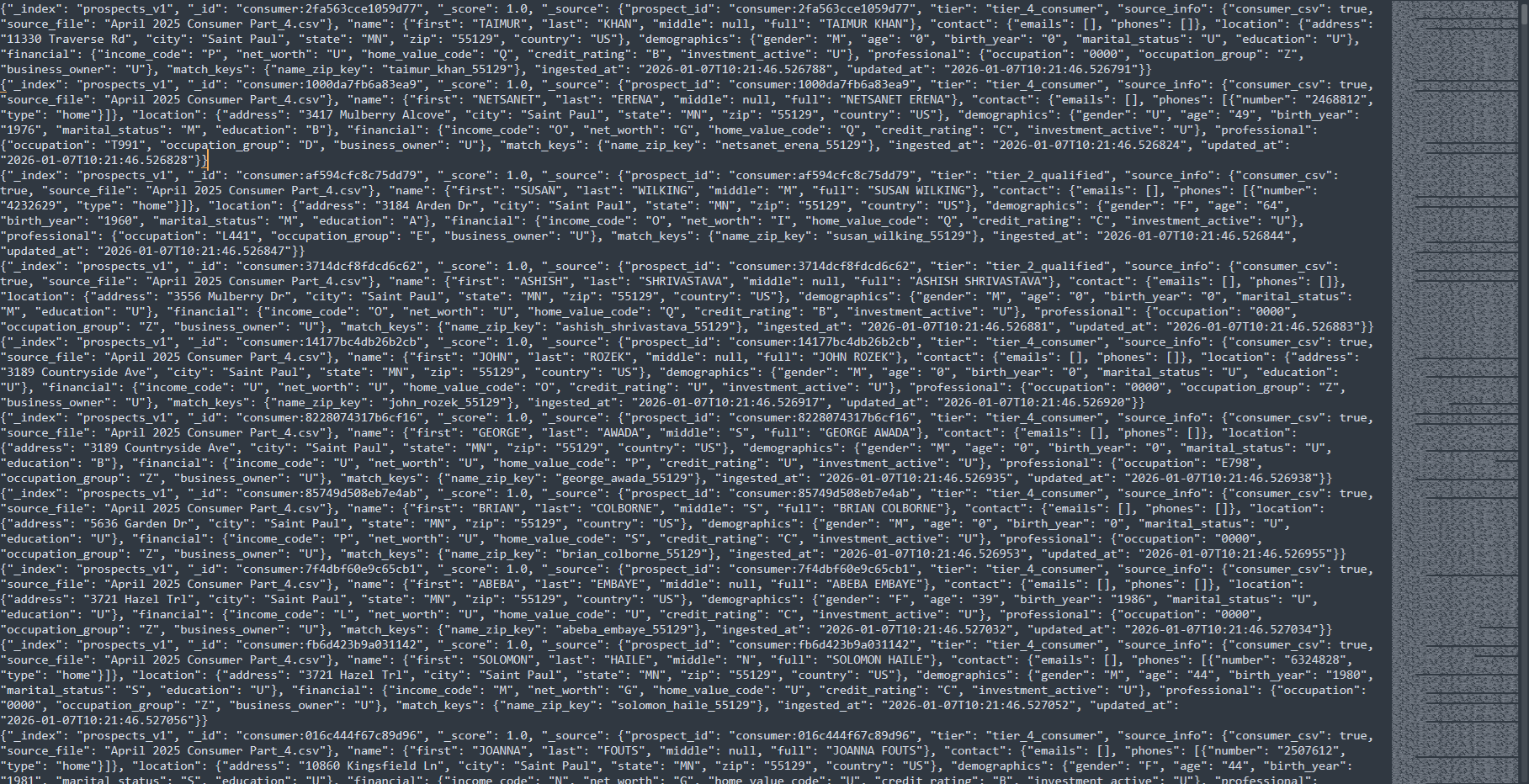
Example fields reportedly included:
| Category | Example Data |
| Name | Full consumer identity |
| Address | Street, city, ZIP, country |
| Demographics | Gender, marital status, education |
| Financial | Credit rating, income code |
| Professional | Occupation classification |
| Metadata | Source CSV references |
| These structured schemas resemble prospect enrichment databases frequently used in marketing analytics or lead intelligence systems. | |
| While emails and phone fields appear partially empty in samples, even partial identity datasets can enable correlation attacks when combined with other breaches. |
Why Large Database Leaks Matter in 2026
Massive exposures like the alleged EquityBrix data leak demonstrate a growing trend: attackers increasingly target aggregated data repositories rather than individual accounts.
Why? Because aggregated datasets multiply value.
Cybercriminals can:
- Build identity profiles
- Enhance phishing campaigns
- Perform account takeover attempts
- Conduct financial fraud analysis
- Sell segmented consumer intelligence
According to cybersecurity guidance from the National Institute of Standards and Technology, organizations must prepare to detect, respond to, and recover from confidentiality attacks due to their financial and reputational consequences. (NIST)
This aligns with modern risk models where exposed metadata alone can become actionable intelligence.
How the Leak Was Discovered on Dark Web Forums
The discovery occurred during routine threat-intelligence scanning performed by the Kaduu team. Platforms like DarknetSearch monitoring platform continuously scan underground markets, forums, Telegram channels, and botnet logs for newly published datasets.
Such monitoring systems rely on automated crawling combined with analyst validation workflows. Continuous intelligence collection enables early identification of threats before mainstream disclosure.
Organizations increasingly deploy services like:
- Dark web intelligence reports
- Threat monitoring dashboards
These approaches allow analysts to verify claims, assess risk exposure, and alert affected entities rapidly. 🧠
This is where proactive data breach detection becomes critical — identifying exposures before attackers operationalize them.
Potential Risks for Individuals and Businesses
Even when sensitive fields appear incomplete, large datasets can still generate significant downstream risks.
Individual Risks
- Identity correlation across breaches
- Targeted phishing attempts
- Social engineering attacks
- Fraud profiling
Business Risks
- Compliance violations
- Legal exposure
- Loss of customer trust
- Increased cyber insurance costs
This is why cybersecurity experts emphasize layered visibility rather than reactive incident handling alone. The alleged incident underscores how brand reputation can be affected even before confirmation, making brand protection strategies essential.
Question: Is the Leak Verified?
Short answer: Not yet fully confirmed.
Alleged leaks appearing on underground forums require verification through:
- Data sampling validation
- Source attribution analysis
- Hash or schema comparison
- Victim confirmation processes
Until confirmation occurs, the dataset should be treated as an alleged exposure rather than a proven breach. However, early awareness allows organizations to prepare defensive measures.
Checklist: What Organizations Should Do Immediately ✅
If your company suspects inclusion in a similar dataset, follow this practical checklist:
- Monitor underground forums continuously
- Validate exposed records quickly
- Reset exposed credentials where applicable
- Notify internal security teams
- Conduct forensic analysis
- Update incident response workflows
- Communicate transparently with stakeholders
NIST incident-response guidance emphasizes preparation and structured recovery planning as key components of resilience. (NIST)
Proactive response dramatically reduces long-term impact.
The Growing Role of Dark Web Intelligence
Cybercrime marketplaces now operate with professional efficiency. Actors publish leaks strategically to maximize visibility and resale opportunities.
A modern dark web solution integrates:
- Automated crawling
- AI-based classification
- Analyst verification
- Real-time alerts
- Risk scoring models
Threat intelligence is no longer optional — it is a core cybersecurity function. Organizations using continuous monitoring often discover exposures weeks earlier than those relying solely on public breach notifications. 📊
This shift explains why dark web monitoring has become a central component of enterprise security architecture.
Understanding the Structure of Prospect Databases
The sample schema linked to the alleged EquityBrix data leak reveals insights into how consumer datasets are structured.
Typical enrichment datasets include:
- Identity normalization keys
- Geographic clustering
- Financial scoring indicators
- Marketing segmentation tiers
These datasets are valuable because they aggregate multiple public and commercial data sources into a unified profile.
When exposed, attackers gain pre-organized intelligence without needing to compile information themselves — dramatically lowering attack costs.
Expert Perspective on Large-Scale Exposure
Cybersecurity analysts frequently note that data aggregation platforms represent high-value targets.
“The more structured the dataset, the more operational value attackers gain,” explains threat-intelligence professionals studying large forum leaks.
Structured consumer intelligence databases can accelerate fraud automation and targeted social engineering campaigns.
The scale alone — over 152 million records — positions this alleged event among the largest forum listings observed recently.
Long-Term Implications for Cybersecurity Strategy
Incidents like the alleged EquityBrix data leak reinforce three major industry trends:
- Data concentration increases breach impact.
- Underground forums remain primary leak distribution channels.
- Early detection determines response success.
Organizations moving toward continuous intelligence monitoring reduce detection time significantly compared to traditional approaches.
Modern cybersecurity must combine:
- external threat intelligence
- exposure monitoring
- proactive risk assessment
- continuous verification workflows
These layers transform security from reactive defense into predictive risk management. 🛡️
Conclusion: Why Early Awareness Matters
Whether fully verified or still under investigation, the alleged EquityBrix data leak demonstrates how quickly massive datasets can surface within underground ecosystems. Early discovery by monitoring teams highlights the importance of visibility beyond traditional security perimeters.
Companies that monitor dark web activity gain critical time to investigate, mitigate risks, and communicate responsibly before incidents escalate. Waiting for official confirmation often means reacting too late.
Organizations should strengthen monitoring capabilities, refine incident response plans, and adopt intelligence-driven security strategies to reduce exposure risk.
👉 Discover much more in our complete guide
👉 Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →

