Data Breach Revealed: 300K Records in VUMI Insurance Leak

➤Summary
A major data breach allegedly involving VUMI Group Insurance has surfaced on underground forums, raising serious concerns about data security and privacy. According to a post published on Darkforums.su by a user known as “ByteToBreach” on April 13, 2026, sensitive data from hundreds of thousands of individuals may have been compromised. This incident underscores the rising importance of dark web surveillance and proactive cybersecurity strategies. As organizations face increasingly sophisticated threats, mastering healthcare data breach detection—along with understanding how breaches occur and how to respond effectively—has become essential. This darknetsearch.com article explores the details of the alleged breach, its potential impact, and how businesses and individuals can protect themselves using tools like real-time dark web monitoring solution and underground forum monitoring.
What We Know About the Alleged Breach 🧠
The claims suggest that the attacker exfiltrated data over a period of six days, using methods designed to avoid detection and prevent server crashes. The breach reportedly includes:
- Around 300,000 insured individuals
- Over 25,000 staff, partners, and agents
- Complete personally identifiable information (PII)
- Social Security Numbers (SSNs)
- Passport documents
- W-9 forms

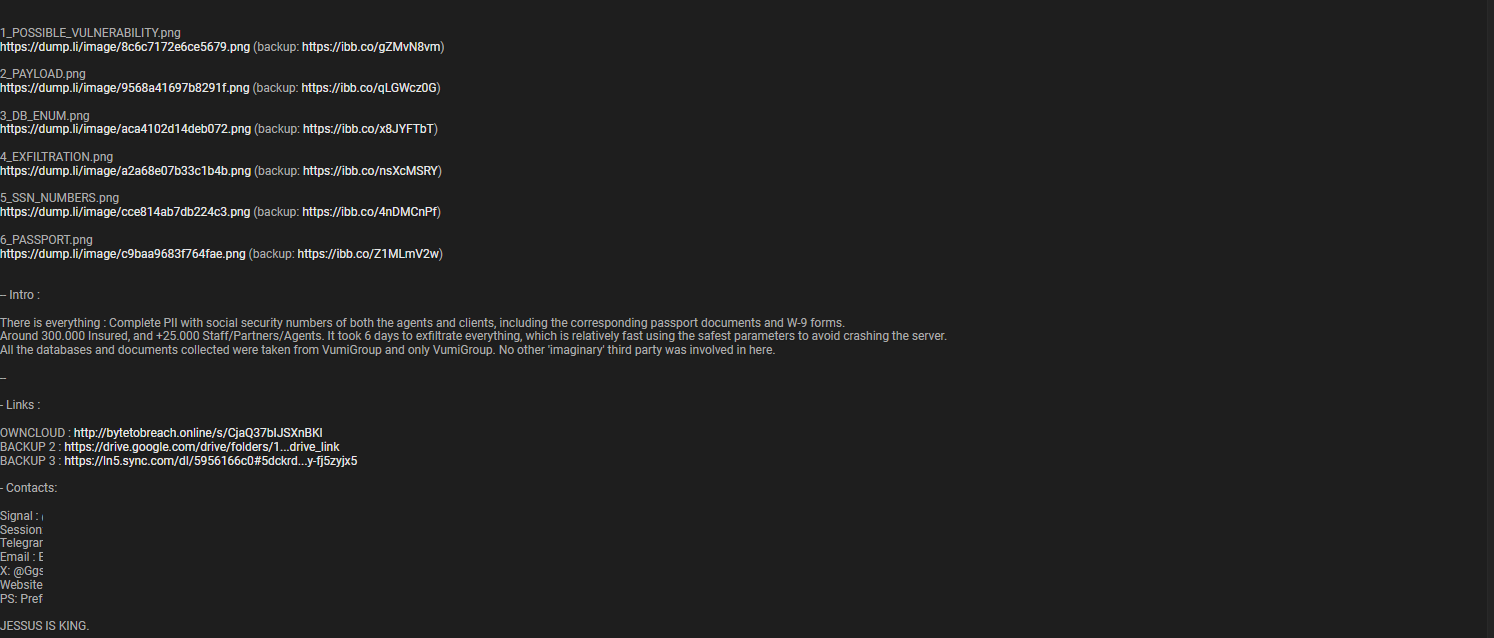
The attacker also claims that all data was sourced directly from VUMI Group systems, with no third-party involvement. While these claims are yet to be independently verified, the scale and sensitivity of the data raise serious red flags.
Why This Data Breach Is Particularly Dangerous ⚠️
Not all breaches are equal. This one stands out due to the type of data allegedly exposed. SSNs, passport copies, and tax forms are among the most sensitive data types.
This creates multiple risks:
- Identity theft and financial fraud
- Targeted phishing campaigns
- Credential stuffing attacks
- Long-term reputational damage
Unlike passwords, this kind of data cannot easily be changed. This makes real-time dark web monitoring solution essential for early detection and response.
How Attackers Likely Operated 🔐
Although technical details are limited, the attacker’s statement suggests a methodical and stealthy approach. The six-day exfiltration timeline indicates:
- Controlled data extraction to avoid detection
- Possible use of privileged access
- Avoidance of system overload to remain unnoticed
This aligns with modern cyberattack strategies where attackers prioritize persistence over speed. Underground forum monitoring often reveals similar tactics used in high-value breaches.
Indicators Your Data Might Be Compromised 🔍
If you are a client, agent, or partner associated with VUMI, you may be wondering: how to check if my data is on the dark web?
Here are some warning signs:
- Unusual login attempts on your accounts
- Unexpected password reset emails
- Financial activity you don’t recognize
- Alerts from security tools
Using services like Darknetsearch.com can help identify whether your credentials or personal data have appeared in dark web marketplaces.
The Role of Dark Web Surveillance 🌐
Dark web surveillance is a critical defense mechanism in today’s threat landscape. It involves scanning hidden forums, marketplaces, and encrypted channels for stolen data.
Key benefits include:
- Early detection of leaked credentials
- Identification of emerging threats
- Protection against identity theft
Platforms such as Darknetsearch.com provide continuous visibility into potential risks, allowing organizations to act before damage escalates.
Underground Forum Monitoring Explained 💻
Underground forum monitoring focuses specifically on tracking hacker communities where stolen data is often shared or sold.
These forums:
- Act as marketplaces for breached data
- Provide insights into attacker behavior
- Reveal new attack techniques
By leveraging underground forum monitoring, organizations can gain intelligence that traditional security tools might miss.
How to Prevent Credential Stuffing Attacks 🛡️
One of the biggest risks following a data breach is credential stuffing. This occurs when attackers use stolen credentials to access other accounts.
To mitigate this risk:
- Enable multi-factor authentication (MFA)
- Use unique passwords for each account
- Monitor login activity
- Implement credential stuffing prevention tools
Organizations should also invest in threat detection systems that integrate with real-time dark web monitoring solution platforms.
Practical Checklist for Immediate Protection ✅
Here’s a quick checklist to protect yourself after a potential data breach:
- Change all your passwords immediately
- Enable MFA on critical accounts
- Monitor your financial statements
- Use a real-time dark web monitoring solution
- Check for leaked data using trusted tools
- Stay alert for phishing attempts
This proactive approach can significantly reduce your risk exposure.
Expert Insight 💬
Cybersecurity experts often emphasize the importance of visibility. As one analyst noted, “You can’t defend against what you can’t see.” This is why combining dark web surveillance with threat intelligence is essential in modern cybersecurity strategies.
The Growing Need for Proactive Security 📊
The VUMI incident—if confirmed—demonstrates how quickly sensitive data can be exfiltrated and distributed. Organizations must move beyond reactive security and adopt proactive measures.
This includes:
- Continuous monitoring
- Threat intelligence integration
- Employee awareness training
- Investment in advanced detection tools
What Should You Do Next? 🤔
If you suspect your data may be involved in this breach, act immediately. Don’t wait for confirmation.
Question: What is the fastest way to protect yourself after a data breach?
Answer: Change your passwords, enable MFA, and use a real-time dark web monitoring solution to detect misuse of your data.
Taking quick action can make a significant difference in preventing further damage.
Conclusion: Stay Ahead of Cyber Threats 🚀
The alleged VUMI Group Insurance data breach is a stark reminder of the evolving cyber threat landscape. With sensitive data potentially affecting over 300,000 individuals, the risks are substantial.
Whether verified or not, this incident underscores the importance of dark web surveillance, underground forum monitoring, and credential stuffing prevention. Organizations and individuals alike must adopt a proactive approach to cybersecurity.
Don’t wait until it’s too late—take control of your digital security today.
👉 Discover much more in our complete guide
👉 Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →

