Aramco Data Breach: 68K Workforce Records Exposed

➤Summary
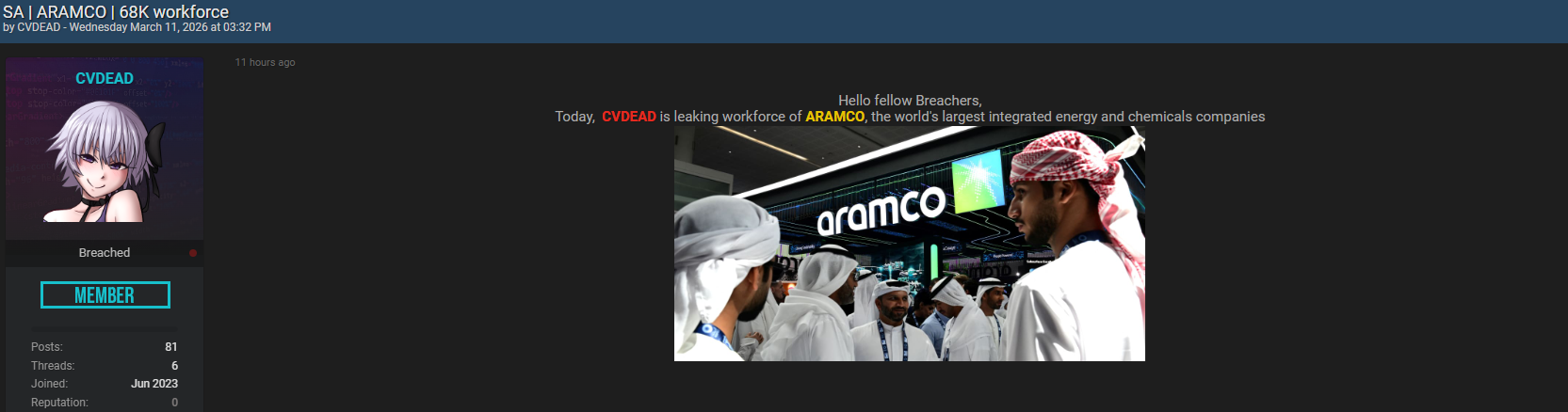
The Aramco data breach has surfaced as a significant cybersecurity concern after an alleged dataset involving approximately 68,000 workforce records appeared on Breachforums.as. The listing, reportedly posted on March 11, 2026, by a threat actor known as “CVDEAD,” claims to contain sensitive employee information connected to Saudi Arabia’s energy giant Saudi Aramco. Although the claims remain unverified at the time of writing, cybersecurity experts warn that workforce-related exposures carry heightened risks due to identity verification data and employment records. 🛢️
Incidents involving critical infrastructure organizations attract global attention because attackers often exploit leaked information for espionage, financial fraud, or targeted social engineering. This darknetsearch.com article examines the alleged exposure, the structure of the compromised data, possible risks, and recommended defensive measures organizations and employees should consider.
Alleged Breach Overview and Forum Disclosure
According to the Breachforums.as post, the threat actor advertised a database allegedly linked to Aramco workforce records. The listing included structured employee information fields and suggested access to internal personnel datasets.
Reported details:
- Forum: Breachforums.as
- Author: CVDEAD
- Posted date: 11.03.2026
- Alleged scope: 68K workforce records
Forum disclosures often act as early indicators of potential breaches. Threat actors commonly publish listings to validate possession of data or attract buyers before wider distribution.
Government agencies such as the Cybersecurity & Infrastructure Security Agency emphasize monitoring underground sources as part of modern threat detection strategies (https://www.cisa.gov).
Structure of the Allegedly Compromised Data
The forum post describes a dataset containing workforce identity and employment information. The fields reportedly include:
- NIN (National Identification Number)
- ExId
- First Name (FName)
- Second Name (SName)
- Third Name (ThdName)
- Last Name
- Date of Birth
- Citizenship
- Residency status
- Broker Account Number
- Residential Country
- Hire Date
This combination represents highly sensitive personal and employment data. Unlike typical consumer breaches, workforce datasets may enable deeper identity verification attacks due to official identifiers.

Why Workforce Data Is Highly Valuable
Employee records are among the most sought-after datasets in cybercrime ecosystems. Attackers value workforce information because it allows precise targeting.
Common exploitation scenarios include:
- Identity impersonation using national IDs
- Executive phishing campaigns
- Financial account fraud
- Insider threat simulation
The alleged Aramco data breach illustrates how workforce databases can provide attackers with contextual intelligence about organizational structures.
Potential Risks to Employees
If the dataset proves authentic, employees could face several cybersecurity risks:
- Targeted spear-phishing emails referencing employment details.
- Identity fraud leveraging national identification numbers.
- Account takeover attempts using personal verification data.
- Financial scams involving broker account references.
Because workforce records often include verified identity attributes, attackers can craft highly convincing communications. 🔐
Organizational Security Risks
Beyond individual exposure, workforce leaks can create enterprise-level risks:
- Social engineering against internal departments
- Credential harvesting campaigns
- Supply-chain infiltration attempts
- Corporate espionage targeting strategic staff
Energy sector organizations remain frequent targets due to geopolitical and economic importance.
Question & Answer
Why are workforce breaches more dangerous than customer breaches?
Workforce datasets often contain verified identity and employment details that attackers can use to bypass authentication checks or impersonate trusted personnel.
The Role of Underground Forums in Breach Disclosure
Cybercrime forums function as marketplaces and signaling platforms. Once data appears publicly, threat actors may:
- Validate dataset samples.
- Sell access to multiple buyers.
- Launch coordinated phishing campaigns.
- Use publicity to pressure organizations.
Security teams increasingly deploy monitoring platforms such as https://darknetsearch.com/ to detect mentions of company data appearing in underground environments.
A proactive Darknet Threat Intelligence Solution enables early detection of leak claims before large-scale exploitation occurs. 🚨
Indicators Organizations Should Monitor
Companies should watch for warning signs following alleged exposures:
- Unusual login attempts targeting employees.
- Suspicious emails referencing employment data.
- Increased phishing reports.
- Unauthorized credential reset requests.
Early monitoring can significantly reduce operational impact.
Technical Risk Analysis
The alleged dataset contains multiple identity verification attributes, making it particularly sensitive.
| Data Element | Potential Risk |
| NIN | Identity theft |
| Date of Birth | Verification bypass |
| Phishing attacks | |
| Broker Account Number | Financial targeting |
| Hire Date | Organizational profiling |
| Such structured datasets allow attackers to build detailed identity profiles. |
Industry Context: Critical Infrastructure Targeting
Energy companies have historically faced advanced cyber threats due to their strategic importance. Attackers may pursue workforce information not only for financial gain but also for intelligence gathering.
Cybersecurity analysts note a shift toward targeting human infrastructure rather than technical systems. 👨💻
Expert Insight
A threat intelligence analyst explained:
“Modern cyberattacks focus on people as entry points. Workforce data enables attackers to weaponize trust.”
This reflects why employee datasets are increasingly valuable within cybercriminal markets.
Practical Protection Checklist
Employees and organizations should implement the following safeguards:
✅ Change passwords linked to corporate and personal accounts
✅ Enable multi-factor authentication
✅ Verify unexpected communications carefully
✅ Report suspicious emails immediately
✅ Monitor financial and identity accounts
✅ Conduct employee awareness training
Practical tip: attackers frequently impersonate HR departments after workforce leaks.
Incident Preparedness and Response Strategies
Organizations must prepare structured response plans even before breach confirmation. Effective incident response includes:
- Threat intelligence monitoring
- Communication transparency
- Credential resets
- Access review audits
- Continuous log analysis
Rapid containment reduces downstream exploitation risk and preserves organizational trust. 🛡️
What Happens Next?
Possible developments following the forum listing include:
- Official confirmation or denial after investigation.
- Independent verification by cybersecurity researchers.
- Regulatory reviews depending on jurisdiction.
- Increased social engineering campaigns referencing the incident.
Users should rely only on official company communications for confirmed updates.
Broader Cybersecurity Lessons
Regardless of verification status, several lessons emerge:
- Workforce data requires strict access control.
- Identity-based security must complement infrastructure defenses.
- Continuous monitoring of underground forums is essential.
- Human-focused security awareness remains critical.
Organizations that combine proactive intelligence with monitoring tools gain earlier visibility into emerging threats.
Conclusion: Awareness Is the First Line of Defense
The alleged Aramco data breach highlights how workforce datasets have become prime targets in modern cybercrime. Even unverified leak claims can lead to real-world risks as attackers exploit uncertainty to launch phishing and impersonation campaigns. Understanding how such incidents unfold enables organizations and employees to respond proactively, strengthening defenses against evolving threats. 🌐
As cyber threats increasingly focus on identity and human trust, continuous monitoring, rapid response planning, and employee awareness become essential pillars of modern cybersecurity resilience. 🔎
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.